In part 3 of this multi-part article we discussed the trojan horse type of malware. Recall from previous articles that the definition of malware is a type of software designed to take over or damage a computer, without the user’s knowledge or approval. Let’s discus the zombie!![]()
A zombie is not actually malware. Computer’s become zombies via malware. A zombie is a computer that is infected with malware that allows remote software updates and control by a command and control center called a zombie master.
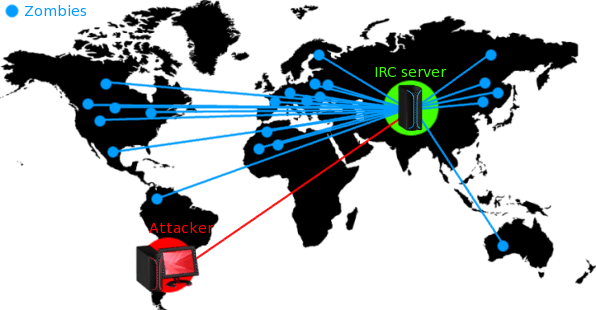
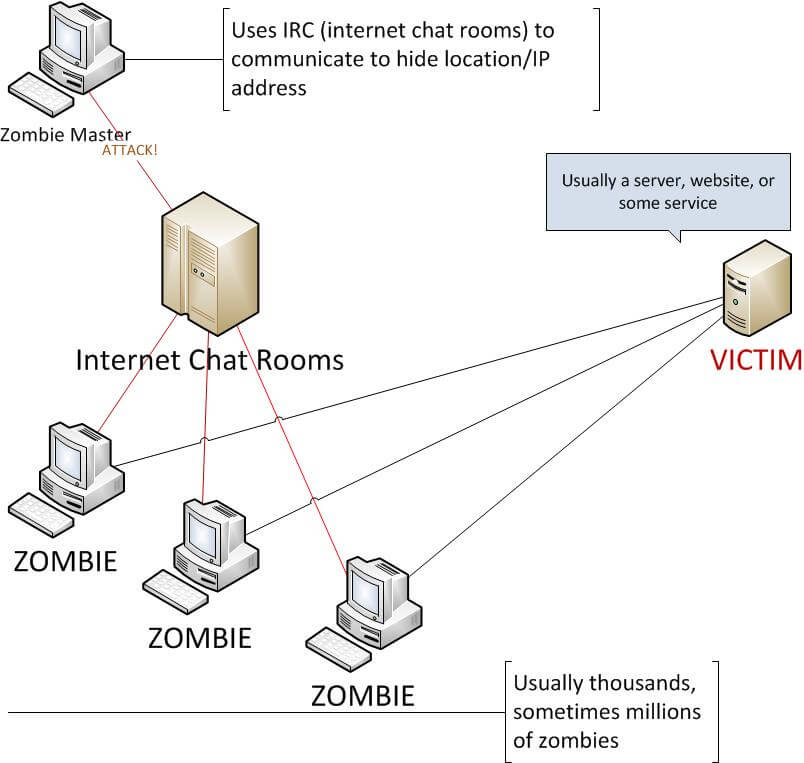
A zombie is also know as a bot, short for robot. Zombies commonly use Internet Relay Chat (IRC) channels (also known as chat rooms) to communicate with the zombie master.
“Zombified” computers are frequently used to aid spammers. They are also used to attack other systems. Zombies are also sometimes used to commit click fraud. The Internet uses a form of advertising, called pay per click, in which the developers of a Web site places clickable links for advertisers on their Web site, and each time the link is clicked on, a charge is generated. Zombie computers can be used to commit click fraud by imitating a legitimate user clicking on an ad to generate fraudulent revenue.
The question that we are often asked is, “Why would they want to get into my computer, there’s nothing there?” Well, here’s the answer to that question. If your computer becomes a zombie, it becomes part of a botnet. We will discuss botnets in our next article. Once your computer becomes a member of a botnet, the zombie master can send a single command to have all zombies attack another system. Meanwhile, YOUR IP address is attached to that attack. The authorites come after YOU, not the attacker.
To help you better understand the whole zombie and botnet concept, here’s an infographic.
As we’ve said before, it’s sometimes very difficult to remove these viruses, so the best defense is prevention. Keep your systems updated with the latest patches for all software you run, and ensure you have the latest anti-virus software definition updates. Avoid clicking on links and opening attachments if you did not expect it to be sent.
Stay tuned for our next article where we will cover the BOTNET. Or, you can subscribe to our newsletter using the form on the right and have our informative articles delivered to you via email once a week.