In part 4 of this multipart article we discussed the Zombie. Recall from previous articles that the definition of malware is a type of software designed to take over or damage a computer, without the user’s knowledge or approval. Let’s discus the BOTNET!
Like the zombie, a botnet is not actually malware. When computer’s become zombies, they often become part of a large botnet. A botnet refers to a group of zombie computers which are commanded from a central control infrastructure. If you missed our last article about zombies, you should read it first to help you understand the botnet concept.
A botnet is:
Under a command and control infrastructure
The zombie master (also known as the bot herder) can send remote commands to order all the bots they control to perform actions. Often, the zombie master will not send commands directly to the bots. Doing so would likely result in detection. So, instead the bots listen to a third party for commands. Often times, the commands are sent using IRC (internet chat) servers in an effort to mask the zombie masters location.
 Detected through the use of firewall
Detected through the use of firewall
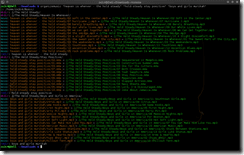
There are many types of firewalls and most firewalls contain logs. These logs must be analyzed by IT professionals to determine if a computer may be acting as a zombie participating in external attacks.
Detecting botnet activity is difficult. It usually requires an IT professional who specializes in cyber security to detect and eliminate this threat. There are automated systems to help detect and attempt to prevent these types of attacks. They are known as IPS (Intrusion Prevention Systems) and IDS (Intrusion Detection Systems). IPS and IDS is sometimes bundled with antivirus software but we have found that they require more than just a basic level of understanding to configure them properly. Otherwise, you have to manually accept or reject each and every connection attempt.
As we have said before, the best defense is prevention. Keep your systems updated with the latest patches for all software you run, and ensure you have the latest anti-virus software definition updates. Avoid clicking on links and opening attachments if you did not expect it to be sent.
Stay tuned for our next article where we will cover the ROOTKIT. Or, you can subscribe to our newsletter using the form on the top right and have our informative articles delivered to you via email once a week.
